📄 GOVERNMENT-SAFE CAPABILITY BRIEF
Controlled Global Entity Discovery Capability
For Government and National-Security Evaluation
Overview
This document describes a controlled-access intelligence capability designed to identify and classify global entities by operational intent, sector exposure, and strategic relevance rather than by self-reported labels or public categorization.
The system is intended for government, national-security, and regulated-use environments where visibility, control, and governance are essential.
The Problem
Governments face persistent blind spots when attempting to:
-
Identify companies involved in sensitive sectors (energy, infrastructure, logistics)
-
Detect indirect or non-obvious exposure to sanctioned or high-risk regions
-
Anticipate which entities will be positioned to participate in large-scale reconstruction or investment efforts
Traditional tools rely heavily on:
-
Static industry codes
-
Public descriptions
-
Manual analysis
These methods are slow, incomplete, and increasingly ineffective.
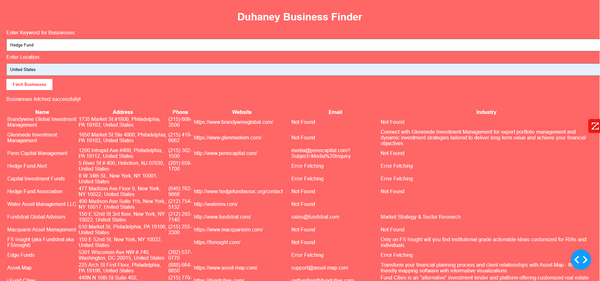
The Capability
This system enables entity discovery by intent and exposure, allowing evaluators to:
-
Identify companies connected to a sector or region even when not explicitly labeled
-
Surface upstream, midstream, downstream, and support entities
-
Detect foreign and domestic actors with operational, logistical, or financial relevance
The capability is sector-agnostic and has been demonstrated using energy and oil-industry scenarios.
Access Control & Governance
A core design principle is centralized, time-bound access control:
-
Authorization is temporary and revocable
-
No persistent licenses
-
No uncontrolled redistribution
-
Access duration is defined by the controller (hours, days, or longer)
-
Capability is intended to remain under responsible stewardship
This design supports sensitive evaluations and reduces the risk of misuse or uncontrolled proliferation.
Why This Is Sensitive
Unrestricted access to global entity discovery by intent could:
-
Enable sanctions evasion
-
Expose supply-chain vulnerabilities
-
Be misused for market manipulation or intelligence exploitation
For this reason, the capability is not publicly deployed and is made available only for controlled evaluation.
Intended Evaluation Path
-
Initial interest confirmation
-
NDA or equivalent evaluation framework
-
Constrained demonstration using a predefined scenario
-
Determination of suitability for government or contractor stewardship
Status
The capability exists today and is functional.
This document is not a sales pitch but a request for qualified evaluation by appropriate government or prime-contractor entities.